Regardless of where employees are working, they need to be able to access their organization’s resources in Microsoft 365 like apps, files, and data. Hybrid work is more common than ever and employees, contractors, vendors, and partners need secure access to company resources whether they’re working on-site or remotely.
This is where identity and access management (IAM) comes in. Read our blog to learn why IAM is essential in Microsoft 365 and some of the best practices to implement today.
What is Identity and Access Management (IAM)?
Identity and access management (IAM) is a framework of policies and procedures which makes it possible for the right people within and outside of the organization to easily and securely access the right digital assets, including emails, apps, documents, and data.
IT departments can implement these policies and procedures within Microsoft 365 to control users’ access privileges in a hybrid environment across on-premise and cloud-based systems.
The ultimate goal is to assign a single digital identity to each entity accessing the resources, authenticate them upon entry into the environment, authorize them to access specifically permitted resources, and manage those identities throughout their entire lifecycle.
These digital identities extend beyond staff and employees of the organization working on-premise or remotely. Opening systems to customers, contractors, vendors, business partners, and suppliers can increase efficiency and lower costs, therefore IAM practices should take into consideration external access as well.
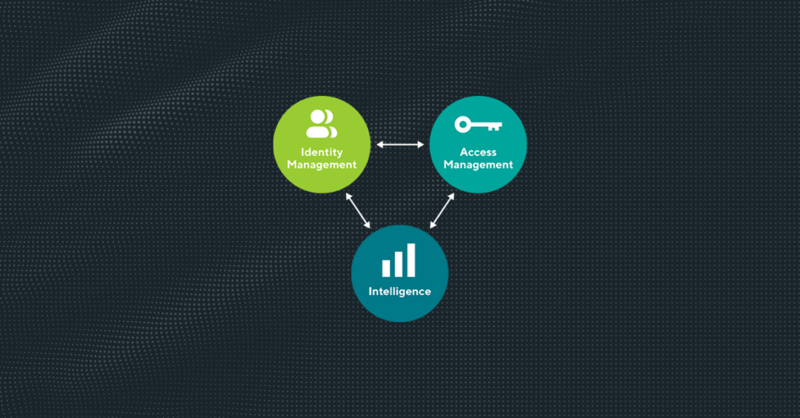
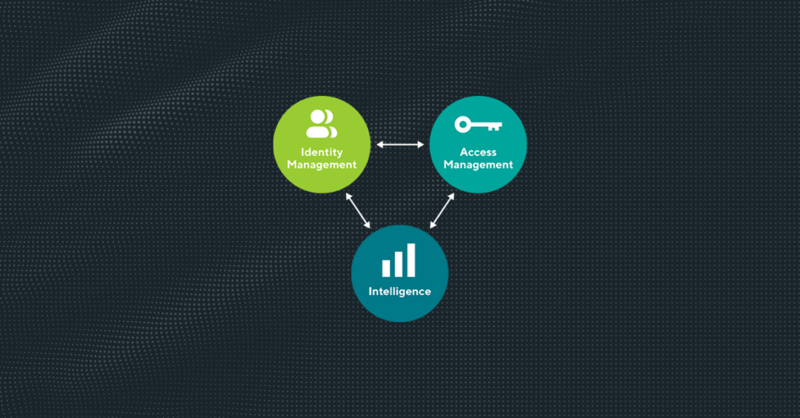
Elements of IAM:
Why is IAM it important?
IAM is an essential part of cybersecurity. Cybercriminals are becoming more evolved and sophisticated each day, and so are their means of attacking organizations.
IAM strikes the right balance between making organizations’ digital assets inaccessible by most, but easily accessible by those who have been granted permission to access them. IAM gives the IT administrators the means to not only set controls for who can access what, but also review existing access and, in a case of a breach, easily revoke access from a compromised user.
While perfect protection, unfortunately, doesn’t exist, IAM solutions are an excellent way to prevent and minimize the impact of attacks. Let’s take a look at the full list of benefits of implementing IAM in your organization.
1. Reduced cost of a potential data breach
According to IBM’s Cost of a data breach 2022 report, the global average cost of a data breach is $4.35M. Some 45% of data breaches occur in the cloud and cloud misconfigurations and vulnerabilities are some of the top key cost factors.
With the increasing amount and value of data being hosted in cloud environments, organizations should take steps to protect cloud-hosted databases. Mature cloud security practices were associated with breach cost savings of USD$720,000 compared to organizations without cloud security practices. IAM is a security practice that has the power to reduce the cost of an average potential data breach by a whopping USD$ 224,396!
2. Enhanced Data Security
By using IAM to manage user access, organizations may stop identity theft, data breaches, and unauthorized access to private company data. Additionally, it can guard against phishing, ransomware, hacking, and other forms of cyberattacks, as well as prevent the spread of compromised login information and unauthorized access to a company’s network.
3. Streamlined IT Workload
Historically, updating access credentials for each user’s account was a constant burden on IT teams. When security policies are altered, all access privileges inside an organization can be changed at once using IAM. IAM can assist in reducing the volume of requests that staff members submit to the IT helpdesk for password resets.
4. Helps in Regulatory Compliance
IAM can help organizations meet the requirements of industry regulations and compliance to ensure the security and privacy of customer data, such as the Health Insurance Portability and Accountability Act (HIPAA), Sarbanes-Oxley (SOX), and the Payment Card Industry Data Security Standard (PCI-DSS).
5. Reduces Human Error
With IAM policies and procedures in place, companies can eliminate manual account and permission errors because the IT department no longer has to manually manage access rights to data.
6. More Effective Access to Resources
Utilizing SSO technology benefits users who gain access through a centralized platform since it reduces the number of encounters they have with security systems and raises the likelihood that they will be successful in accessing the resources they are after.
7. Confidentiality of Data
By restricting access for those who don’t need to use certain apps or files, organizations can better secure sensitive data as well as enable project managers to have a clearer picture of which users are associated with which projects.
8. Helps Manage Access Across Browsers and Devices
One of the many advantages of cloud applications is that users can access them from any internet-connected device. The drawback is that adding new apps also implies adding more URLs and passwords. Additionally, the rise in mobile devices necessitates the management and support of an additional access point by IT administrators.
Cloud-based IAM tools can provide browser-based SSO to all user applications as well as enable access to those same services from users’ mobile devices.
9. Enable secure external access to company’s network
Opening systems to customers, contractors, vendors, business partners, and suppliers can increase efficiency and lower costs. With IAM IT administrators can assign digital identities to third-party organizations and individuals within them, and manage and survey their access more effectively.
10. Streamline Provisioning and Deprovisioning
Deactivating and de-provisioning accounts will be quick and simple with a good IAM system, especially in the event that an employee leaves the organization. When a user has access to a number of different apps, there may be a delay before their account is deactivated after their last day of employment. IAM reduces the chance of a security compromise by making it simpler to deactivate everything at once.
Microsoft security best practices for identity and access management
For Microsoft 365 users, the ultimate answer to all their IAM needs is Azure Active Directory.
Microsoft Azure Active Directory is an IAM cloud platform that companies can deploy to manage users and groups. It helps secure access to on-premises and cloud applications, including Microsoft web services, such as Office 365, and other non-Microsoft software as a service application. Azure Active Directory works across multiple platforms and devices and integrates with on-premises Active Directory.
Tip 1: Establish a single enterprise directory
Clarity and consistency for all roles in IT and Security are improved by having a single authoritative source for identities. By doing this, the security risk posed by human errors and complicated automated failures is reduced. Teams who need to make changes to the directory can do so in one location with the assurance that their change will be applied globally because there is only one authorized source.
Choose one Azure AD tenant to serve as the organization’s authoritative source for all accounts on Azure.
Tip 2: Implement Azure RBAC
Azure role-based access control (Azure RBAC) allows for the fine-grained management of access to Azure resources. You may divide up responsibilities and roles within your team using Azure RBAC, and you can only give users the access they require to do their jobs.
Tip 3: Synchronized identity systems
Identity consistency between cloud and on-premises systems will reduce human errors and the associated security risks. To establish security assurances, teams managing resources in both environments require a consistent authoritative source.
Using hybrid identity, synchronize Azure AD with your current, authoritative on-premises Active Directory Domain Services (AD DS).
Before Azure migration and development initiatives start, this is frequently already completed because it is also necessary for an Office 365 migration.
Tip 4: Implement external sharing and Guest access policies (cloud identity services for third parties)
Use cloud identity services rather than adding vendor, partner, and customer accounts to your on-premises directory to host non-employee accounts.
Giving external parties the proper amount of access rather than the entire default permissions granted to full-time staff lowers security risks. It is simpler to block and identify attacks coming in from these vectors thanks to the least privilege strategy and obvious distinction between external accounts and business workers.
For example, these capabilities natively integrate into the same Azure AD identity and permission model used by Azure and Office 365:
Azure AD for employees and enterprise resources.
Azure AD B2B for business partners.
Azure AD B2C customers or citizens.
We have put together a comprehensive blog on how to enable and disable external sharing in your Azure AD and Microsoft 365 tenant based on every external collaboration business use case.

Tip 5: Passwordless or multi-factor authentication for administrative accounts
Passwordless authentication or multi-factor authentication (MFA) should eventually be implemented for all users, however accounts with administrative rights should be given priority.
By using Managed Identities to allow applications access to resources in Azure, you may decrease the use of passwords by applications.
Want more insights like this one?
For more Microsoft 365, SharePoint Online, and Teams insights, tips and tricks, best practices, and exclusive events delivered straight to your inbox, join our mailing list today and level up your Microsoft 365 game!
/HubSpot%20-%20eBook%20-%20Proof%20Card%20Mockup%20001.jpg?length=10&name=HubSpot%20-%20eBook%20-%20Proof%20Card%20Mockup%20001.jpg)
/HubSpot%20-%20eBook%20-%20Proof%20Card%20Mockup%20001.jpg?length=10&name=HubSpot%20-%20eBook%20-%20Proof%20Card%20Mockup%20001.jpg)
/HubSpot%20-%20eBook%20-%20Proof%20Card%20Mockup%20001.jpg?length=10&name=HubSpot%20-%20eBook%20-%20Proof%20Card%20Mockup%20001.jpg)
/HubSpot%20-%20eBook%20-%20Proof%20Card%20Mockup%20001.jpg?length=10&name=HubSpot%20-%20eBook%20-%20Proof%20Card%20Mockup%20001.jpg)


/HubSpot%20-%20eBook%20-%20Proof%20Card%20Mockup%20001.jpg?length=10&name=HubSpot%20-%20eBook%20-%20Proof%20Card%20Mockup%20001.jpg)

/HubSpot%20-%20eBook%20-%20Proof%20Card%20Mockup%20001-min.jpg?length=10&name=HubSpot%20-%20eBook%20-%20Proof%20Card%20Mockup%20001-min.jpg)
/HubSpot%20-%20eBook%20-%20Proof%20Card%20Mockup%20001-min.jpg?length=10&name=HubSpot%20-%20eBook%20-%20Proof%20Card%20Mockup%20001-min.jpg)